I molntjänster måste du fästa större uppmärksamhet vid informationens konfidentialitet (t.ex. e-post).
Universitetet erbjuder flera krypteringsalternativ. I de här anvisningarna berättar vi om ett flexiblare alternativ för personer som hanterar mycket konfidentiell information. Det här sättet ska tas i bruk enligt rekommendation av exempelvis chefen eller Helpdesk..
Om du inte har särskilda skäl att använda denna krypteringsmetod ska du använda ett lättare alternativ:
- Läs mer om den lättare krypteringsmetoden.
- Läs mer om andra krypteringsalternativ vid universitetet.
All kommunikation behöver inte krypteras.
Använd kryptering när du hanterar skyddat material. Mer detaljerade klassificeringar i Flamma.
Snabbinstruktion
Detaljerad hjälp
Instruktioner för användning av S/MIME-kryptering för Mac. Steg 1, 2 och 5 behöver endast göras en gång.
Krypterad e-post kan skickas och läsas enligt beskrivningen i dessa anvisningar endast på datorer där det installerats ett certifikat!
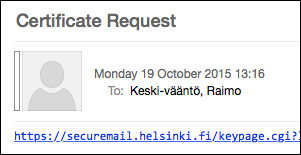
1. Beställning av certifikat
Skicka ett (tomt) e-postmeddelande till adressen smime-request@helsinki.fi.s.
Efter en stund får du ett e-postmeddelande från samma adress med rubriken Certificate Request. Meddelandet innehåller en länk till adressen securemail.helsinki.fi. Klicka på länken.
Observera att länken på grund av säkerhetsskäl BARA fungerar en gång!
Ett fönster öppnas där du ska skapa ett lösenord för certifikatet.
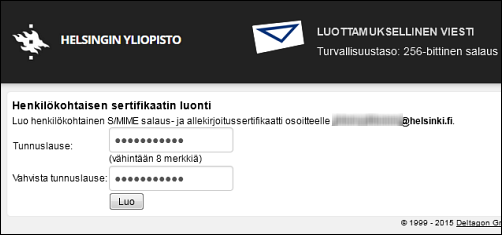
Skriv in lösenordet (två gånger för att bekräfta) och klicka på Create (Skapa).
Kom ihåg att spara lösenordet för framtida användning, eftersom du behöver lösenordet bland annat när du byter dator.
Certifikatet laddas ner till mappen Downloads (Nedladdningar) på datorn.
2. Import till Mac
 Öppna Keychain Access (Nyckelknippe). Du hittar detta via Applications (Program) > Utilities (Tilläggsprogram).
Öppna Keychain Access (Nyckelknippe). Du hittar detta via Applications (Program) > Utilities (Tilläggsprogram).- Klicka på File (Arkiv) > Import Items... (Importera objekt...) och sök efter certifikatet som precis skapats i Downloads (Nedladdningar) (.p12-fil). Välj Login (Inloggning) i rullgardinsmenyn Destination Keychain (Målnyckelknippe). Klicka på Open (Öppna).
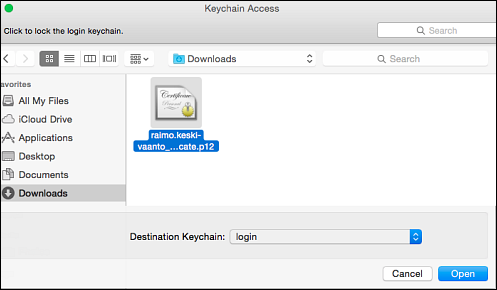
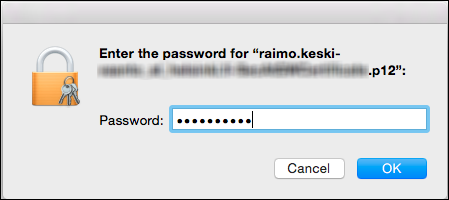
- Därefter uppmanas du att ange lösenordet för certifikatet (som skapades i punkt 1).
Markera certifikatet som betrott
Apple har markerat de certifikat som finns färdigt installerade i systemet som betrodda, men certifikat som du själv importerat är inte automatiskt betrodda. Därför måste du själv markera certifikatet som betrott. Gör så här:
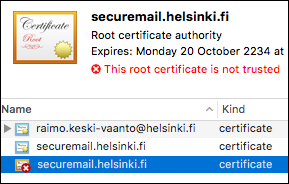
- När du har importerat ett certifikat som du skapat har tre certifikat dykt upp i nyckelknippet Certificates.
- Högerklicka på rotcertifikatet, som har ett rött kryss på kuvertikonen.
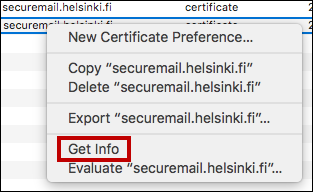
- Välj Get Info (Visa information) i menyn som öppnas.
- En mer detaljerad beskrivning av certifikatet öppnas. Klicka på pilen framför texten Trust (Förtroende), så får du fram en exaktare lista.
- Välj Always trust (Alltid betrott) i rullgardinsmenyn under When using this certificate (Vid användning av detta certifikat). Om du inte gör detta val kommer det att gå att använda certifikatet på datorn, men du får felmeddelanden.
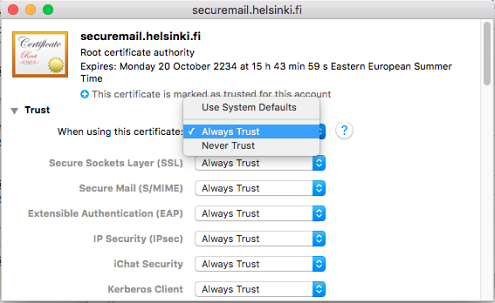
- Stäng fönstret med rotcertifikatet (via den röda cirkeln i det vänstra hörnet). Systemet ber då om godkännande. Signera med lösenordet för ditt användarnamn (inte med lösenordet för certifikatet).
Rotcertifikatet och den förtroendekedja som utgår från det har nu godkänts på denna dator.

Justera därefter inställningarna i det e-postprogram som du använder:
Mac Mail
Starta om datorn och Mail-programmet en gång. Inga ytterligare justeringar krävs. Gå till punkt 3 (Beställa certifikat för mottagaren).
Microsoft Outlook:
- Öppna Outlook > Preferences och välj Accounts. Välj ditt Helsinki.fi-konto och klicka på Advanced...
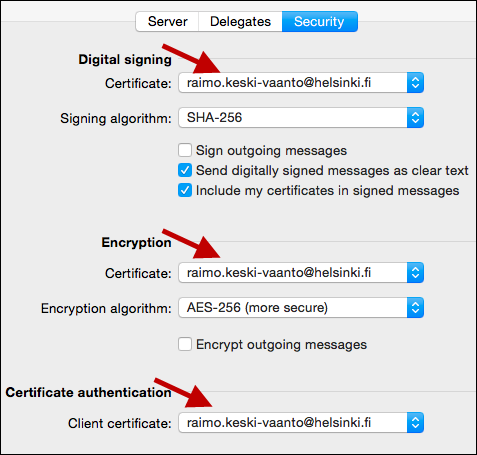
- Välj fliken Security. Välj din e-postadress i rullgardinsmenyn för punkterna Digital signing, Encryption och Certificate authentication. Klicka på OK.
Innan du börjar skicka e-post kan du gärna starta om datorn och Outlook.
Efter omstart av datorn är du redo att skicka krypterad e-post via Outlook. Du kan fortsätta till nästa steg.
3. Beställa certifikat för mottagaren
Du måste beställa ett offentligt certifikat för varje person som du skicka krypterade e-postmeddelanden till.
Skicka e-post till adressen smime-request@helsinki.fi.s med rubriken mottagarens e-postadress.s (t.ex. juhani.pitkanen@helsinki.fi.s).
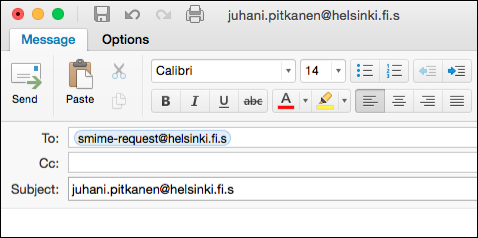
Om en stund får du ett svar.
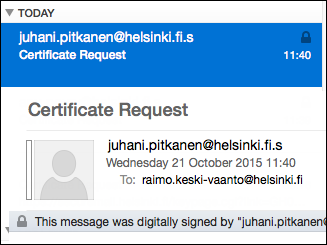
Följande åtgärd är inte obligatorisk, men rekommenderas starkt:
- Klicka på e-postadressen i Certificate Request-meddelandets rubrikfält och välj i Mail Add to Contacts (Lägg till i kontakter) eller i Outlook Open Outlook contact... (Öppna kontaktperson i Outlook...). I Outlook kan du fortfarande redigera informationen. Kom ihåg att slutligen klicka på Save & Close (Spara och stäng).
4. Skicka krypterat meddelande
När du har beställt certifikat för en mottagare och har sparat personens krypterade e-postadress i dina kontakter (se föregående steg) kan du skicka krypterad e-post till personen. Med andra ord kan en person ha två e-postadresser, en krypterad och en okrypterad adress.
- I Outlook väljer du fliken Options (Inställningar) och klickar på Encrypt (Kryptera meddelande) och Sign (Underteckna meddelandet digitalt).
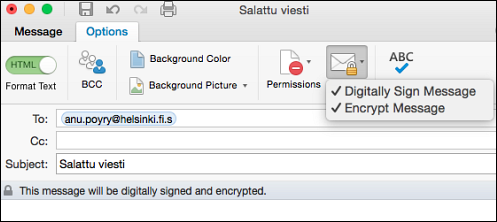
- I Mac Mail visas valen för kryptering och signering automatiskt när e-postadressen slutar på .s. Se till att låset är stängt.
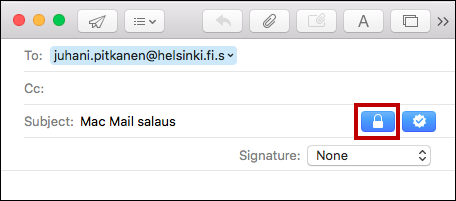
Kontrollera att adressen slutar med .s (3). Adressen finns nu i adressboken, så kom ihåg att kontrollera att du väljer adressen för krypterad e-post.
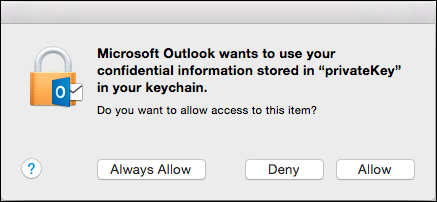
När du klickar på Send (Skicka), frågar Outlook ännu om nyckeln får användas. Välj Allow. Om du vill kan du också välja Always Allow, så får du inte längre denna förfrågan.
5. Förvara certifikatet
Certifikatet är som ett identitetskort. Förvara det med omsorg.
Certifikatet ska förvaras med omsorg. Förvara det inte okrypterat på din arbetsdator, utan helst på ett KRYPTERAT USB-minne(instruktioner för krypterade USB-minnen). Ett annat tillräckligt säkert alternativ är en lösenordsskyddad zip.fil (anvisningar för lösenordsskyddade .zip-filer) som sådan på en nätverksdisk vid universitetet, som endast du har tillgång till. Kom då ihåg att också använda ett tillräckligt starkt lösenordsskydd.
Om certifikatet försvinner ska det upphävas och datasäkerheten skapar ett nytt certifikat för användaren. E-postmeddelanden som krypterats med det gamla certifikatet blir då permanent oläsbara. Om du har problem med certifikatet, kontakta Helpdesk.
Kom ihåg att man inte bör kryptera e-post i onödan. Kryptera endast meddelanden som behandlar konfidentiella frågor.
6. Problemsituationer
Du kan läsa krypterade meddelanden, men det står Unable to verify message signature längst upp.
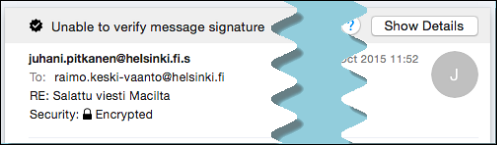
Åtgärd: Gör certifikatet betrott på datorn.
Microsofts anvisningar
Videoinstruktion
Ge respons
Webbplatsen med anvisningar från IT-Helpdesk vid Helsingfors universitet hjälper dig i dina jobbrelaterade IT-frågor. Berätta för oss hur vi skulle kunna förbättra våra anvisningar. Vi uppskattar verkligen din respons!
Hur skulle du förbättra denna instruktion?